Reward yourself for your experience.
Careers
In addition to dynamic career opportunities around the globe, you’ll receive a highly competitive salary, excellent benefits, professional development, and a fully vested 401k.

Jobs Find Me!
We can help find the jobs that fit your skills and interests. We’ll remember your selections and recommend jobs that fit you!
Current Employees
Click the button below to login to your Dayforce Dashboard. Then, click Careers to Search and Apply for current openings.
Prospective Agency/ Supplier Partnerships
Life at All Native
At All Native Group, we’re a family. Our company is owned by the Winnebago Tribe of Nebraska, and just like the tribe, we believe every person is necessary for our continued success.
Our employees work hard to provide the best solutions to our customers while also understanding our underlying mission to support and uplift the Winnebago Tribe
Whether you’re working directly with customers or as an indirect support service, our team thrives together.
Find your next team here.
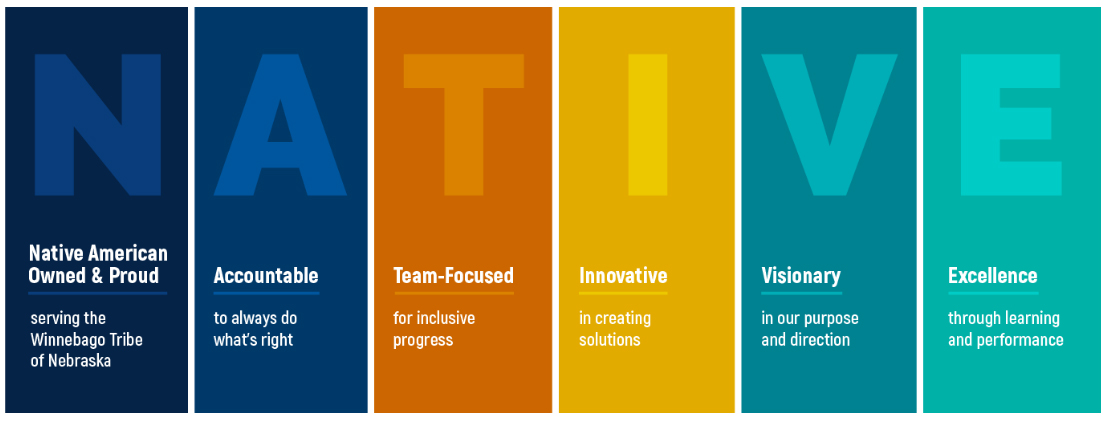
Our Core Values


Our Locations
No matter where you live, we have team members around the world. We pride ourselves in our customer satisfaction and ability to execute contracts. With that mindset, we believe it’s vitally important to be available for our customers—online and on-site.
Search for opportunities in any number of countries including the U.S., Mexico, Egypt, Saipan, Afghanistan, Iraq, Guam, Saudi Arabia, and many more.
Our Benefits
Meaningful and Impactful Work
Our work directly impacts our communities and the Winnebago Tribe of Nebraska. When you work here, your work will contribute to improving the quality of life for our communities.
Medical, Dental and Vision options
Stay healthy with our medical, dental, and vision plans. Choose the plan that works best for you and your family.
Flexible Spending Plan and Healthcare Savings Account (Medical and Dependent care)
Being healthy is important. You can choose between one of two medical care options—Flexible Spending Plan or Healthcare Savings Account.
401(k) Retirement Savings Plan
Save for your future retirement with our 401(k) Retirement Savings Plan. Our plan is straightforward and sets you up for a long, successful retirement. Enrollment occurs in January and July. Participants are fully vested upon enrollment.
Life, AD&D and Disability Insurance
Life is uncertain. That’s why we offer Life, Accidental Death and Dismemberment, and Disability Insurance.
Paid Leave: Company Holiday, Personal (PTO)
We offer a variety of individual leave options that allow you to better balance your work and your life.
Commuter Benefit Program
Commuting can be stressful. We have a Commuter Benefit Program that will make your daily commute more enjoyable.
Education Assistance Program
We strive to employ top talent, and we encourage all employees to continue their education. For employees who take that next step, we offer tuition assistance to help.